Table of Contents
Best BCBS 239 Compliance Tools to Streamline Risk Reporting
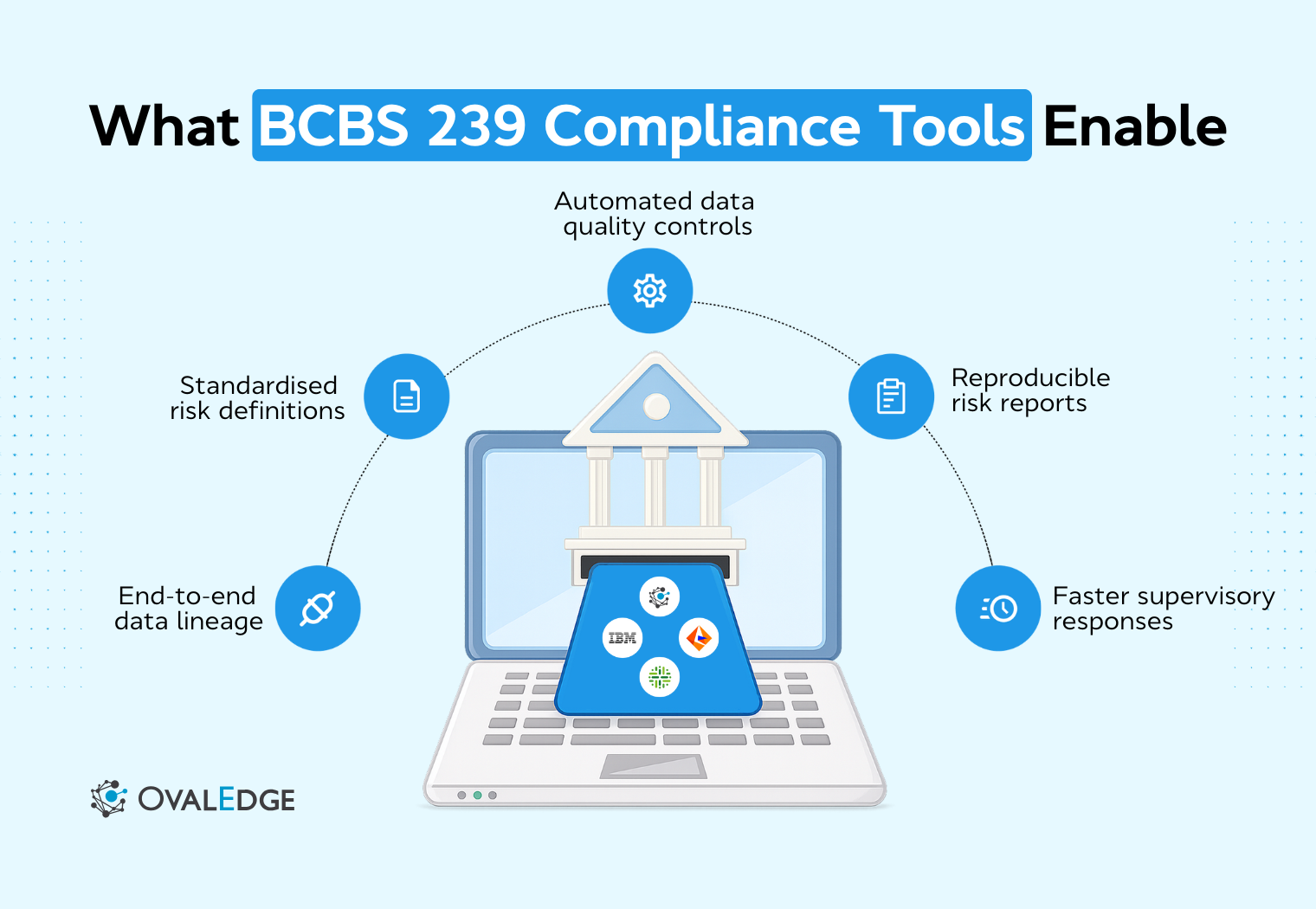
BCBS 239 has evolved into a continuous operating discipline. The article maps key principles to compliance tools across aggregation, governance, lineage, and reporting. It underscores why platforms such as OvalEdge are often used to anchor traceability and accountability, helping institutions demonstrate consistent, audit-ready risk data under normal and stress conditions.
A few years ago, during a regulatory review, a risk team was asked a question that sounded simple. Where did this liquidity risk number come from? The calculation logic was known, and the report was familiar.
But tracing the number back through multiple systems, transformations, and manual adjustments quickly turned into a scramble of spreadsheets and explanations. The problem was not intent or effort. It was the absence of repeatable evidence.
This challenge is not isolated.
As of the most recent Basel Committee assessment, only 2 out of 31 global systemically important banks were assessed as fully compliant with all BCBS 239 principles.
That reality explains why BCBS 239 compliance tools matter today. Expectations have moved beyond documented policies to operational proof. To understand why tools play such a central role, it helps to start with what BCBS 239 compliance actually requires in practice.
What is BCBS 239 compliance?
BCBS 239 compliance is an institution’s ability to meet the Basel Committee’s principles for risk data aggregation and risk reporting by consistently producing accurate, complete, timely, and traceable risk data across all material risk types and legal entities, including during stress events.
In practice, it means risk data can be reliably aggregated, clearly explained, and independently verified through repeatable processes rather than manual explanations or one-off reconciliations.
These requirements are defined through a set of principles that explain how risk data should be governed, aggregated, and reported.
Overview of the Basel Committee’s 14 principles
The 14 principles define what reliable risk data looks like in practice. They focus on outcomes rather than specific technologies and are grouped into three areas:
-
Governance and infrastructure: Require clear ownership, accountability, and demonstrable control over risk data.
-
Risk data aggregation capabilities: Expect risk data to be collected, combined, and adapted across systems and entities without reliance on manual processes, including under stress.
-
Risk reporting practices: Ensure reports are accurate, complete, timely, and consistent, with results that can be reproduced through evidence.
Together, these principles shift attention away from report production and toward whether risk data processes are controlled, scalable, and reliable. Recent assessments show that none of the 14 BCBS 239 principles have been fully implemented across all reviewed institutions, highlighting persistent execution gaps.
Beyond defining principles, BCBS 239 also sets clear expectations for how far risk data controls must extend across the organization.
Scope of risk data aggregation and risk reporting
BCBS 239 applies across the full risk data lifecycle, not just the final report.
-
Source systems: Risk data must be controlled from the point of origin, not reconstructed later.
-
Data transformations and aggregation: All processing steps must be repeatable and traceable, without reliance on manual adjustments.
-
Internal and regulatory reporting: Management and regulatory reports are expected to be consistent or clearly reconciled through evidence.
-
End-to-end traceability: Breaks in traceability upstream are treated as control gaps, even if final reports appear accurate.
The scope reinforces that BCBS 239 is about how risk data is produced, not just how it is presented. The number of banks assessed under BCBS 239 increased from 29 in 2017 to 31 in the most recent review, reflecting sustained supervisory attention over time. This is why BCBS 239 applies consistently across all material risk types.
Applicability across credit, market, liquidity, and operational risk
BCBS 239 applies uniformly across all material risk types and legal entities to ensure risk data is governed, aggregated, and reported consistently, regardless of source or use.
-
Credit risk: data must follow standardized definitions and controls across portfolios and entities.
-
Market risk: data supporting valuations and sensitivities must be traceable and consistently aggregated across systems and reporting views.
-
Operational risk: data, including loss events and scenarios, must be governed with the same rigor as financial risk data, even when sourced manually.
The key expectation is consistency. Differences in control execution across risk types are treated as structural weaknesses, even if individual risk reports appear accurate.
Top 8 BCBS 239 compliance tools for better results
BCBS 239 compliance is proven in execution. Tools matter not because they calculate risk, but because they make risk data traceable, repeatable, and defensible.
They are used to answer the core questions raised in every review: Where did the number come from, how was it produced, who owns it, and can it be reproduced without manual effort.
1. OvalEdge
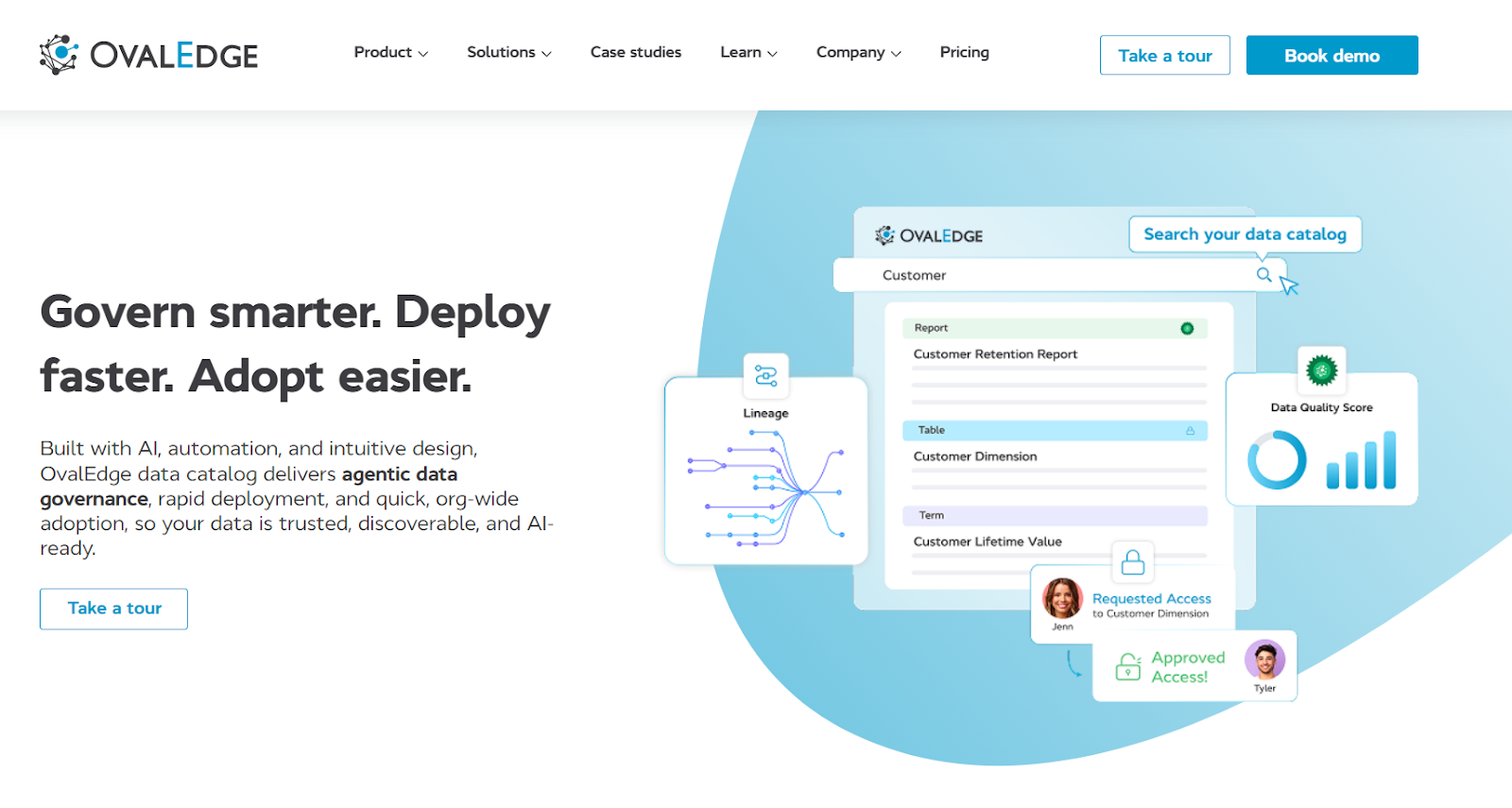
OvalEdge is an enterprise data governance and metadata management platform built to provide visibility into how data is defined, connected, and consumed across complex data ecosystems.
It embeds governance, lineage, data quality, and audit evidence directly into the risk data lifecycle. It also enables institutions to demonstrate how risk data is defined, owned, transformed, validated, and reported through system-generated evidence rather than manual explanation.
How OvalEdge supports BCBS 239 compliance
-
Governance and ownership
Makes ownership and accountability explicit for risk data used in aggregation and reporting. Data owners, stewards, and escalation paths are enforced through workflows, ensuring governance is executed consistently rather than documented informally.
-
Metadata inventory and integration
Automatically extracts and catalogs metadata across source systems, transformation layers, and reporting tools. This creates a unified, continuously updated inventory of risk data assets, eliminating blind spots caused by fragmented environments.
-
End-to-end lineage and traceability
Generates system-driven lineage from source systems to final risk reports. By parsing transformation logic and reporting code, it provides reproducible, column-level traceability that supervisors can review independently.
-
Embedded data quality controls
Enforces data quality checks at the source and during aggregation, with full visibility into downstream impact. Quality issues are detected, monitored, and traced to affected reports through integrated lineage.
-
Audit readiness and evidence
Captures version history, governance decisions, and lineage changes in audit logs that can be reproduced on demand. Lineage reports and governance artifacts can be exported directly for supervisory and internal audit reviews.
-
Role within the BCBS 239 architecture
Complements aggregation and reporting platforms by providing governance, lineage, quality, and evidence layers that they do not establish themselves. It does not calculate risk, but it makes risk results defensible, repeatable, and review-ready.
See how OvalEdge combines governance, data quality, and lineage in a single platform designed for BCBS 239 compliance.
2. Informatica
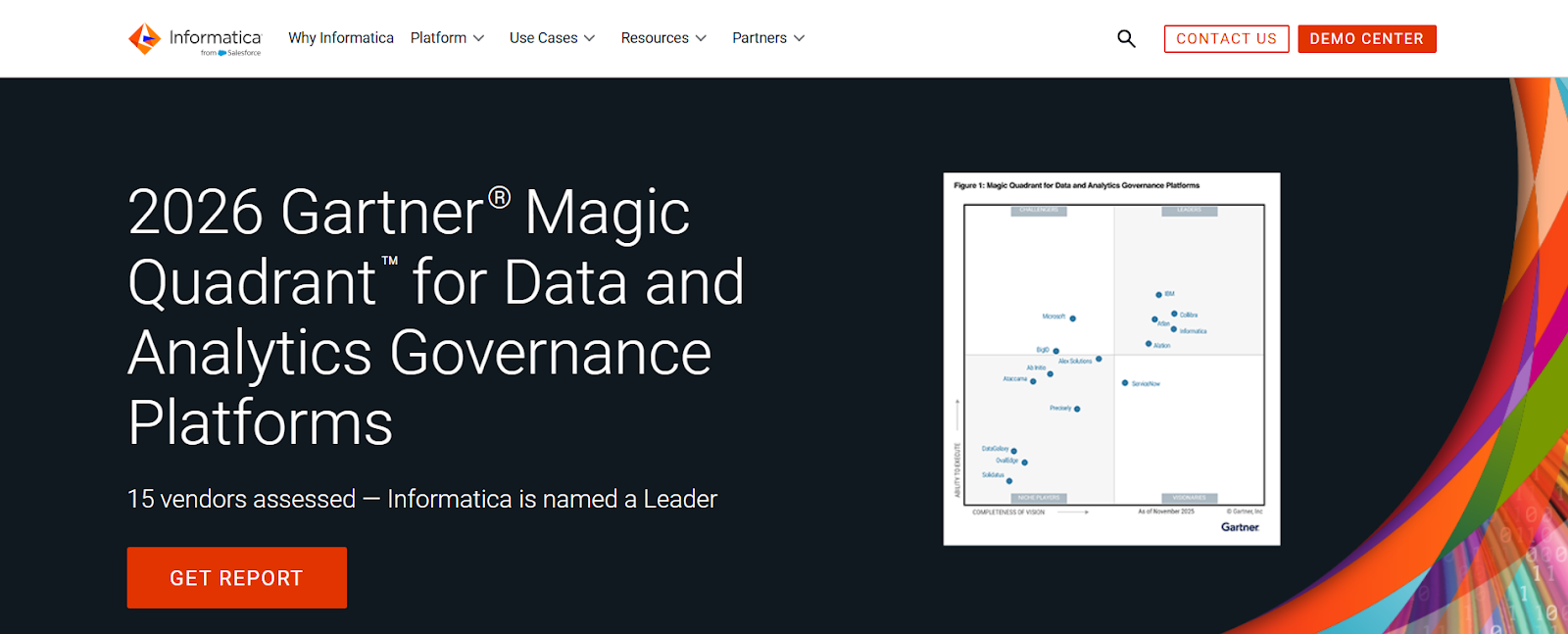
Informatica is an enterprise data management platform focused on data integration, data quality, and transformation across large-scale, distributed environments. It is commonly used where risk data must be extracted from multiple source systems, standardized, and prepared for downstream aggregation and reporting.
How Informatica supports BCBS 239 compliance
-
Standardizes the extraction, transformation, and validation of risk data across multiple source systems, supporting consistent aggregation inputs.
-
Applies configurable data quality rules that help identify accuracy and completeness issues before risk data reaches reporting layers.
Limitation
Customers frequently cite platform complexity and a steep learning curve, which can slow configuration and delay consistent evidence production in early phases.
In BCBS 239 programs, Informatica is most relevant where challenges relate to data movement, validation, and standardization before aggregation, rather than lineage, ownership, or governance across the full risk data lifecycle.
3. IBM
IBM provides enterprise data management, analytics, and regulatory reporting capabilities used across risk, finance, and compliance functions. In BCBS 239 contexts, IBM platforms are often deployed to support centralized data processing, reporting consistency, and control execution across large and complex operating environments.
How IBM supports BCBS 239 compliance
-
Supports large-scale aggregation and reporting through centralized data processing and standardized execution workflows.
-
Generates operational audit trails that help demonstrate consistent control execution over time.
Limitation
Reviews frequently highlight integration complexity across IBM and non-IBM components, increasing operational overhead and coordination effort.
IBM platforms are helpful where the focus is on scalable aggregation, reporting consistency, and operational control execution, rather than end-to-end traceability or governance evidence.
4. SAP
SAP provides enterprise platforms used for finance, risk, and regulatory reporting, with strong integration across core banking, finance, and data environments. In BCBS 239 contexts, SAP is often leveraged where alignment between financial and risk data is a recurring concern.
How SAP supports BCBS 239 compliance
- Aligns finance and risk data using shared enterprise data models, reducing inconsistencies between management and regulatory reporting.
- Supports structured, repeatable reporting workflows that improve consistency across reporting cycles.
Limitation
SAP does not establish enterprise-wide data ownership models or provide cross-system data lineage beyond its own environment, which often requires complementary governance tooling for BCBS 239 evidence.
SAP becomes important in BCBS 239 programs when scrutiny centers on differences between finance and risk numbers and the ability to reconcile them through system-based processes.
5. SAS
SAS is widely used for risk analytics, aggregation, and stress testing across credit, market, and liquidity risk. In BCBS 239 implementations, it is most often associated with the calculation and aggregation layer, especially under stressed conditions.
How SAS supports BCBS 239 compliance
- Supports aggregation of risk exposures and metrics across portfolios, entities, and scenarios, enabling consolidated risk views for management and regulatory reporting.
- Enables repeatable execution of stress tests and scenario analyses under defined assumptions, supporting timely risk reporting during stress periods.
Limitation
SAS does not provide enterprise-wide data governance, ownership models, or end-to-end data lineage across source systems, requiring complementary governance tooling to fully explain data provenance under BCBS 239 reviews.
SAS is most valuable in BCBS 239 contexts where the challenge is producing timely and repeatable risk calculations, rather than proving data lineage or governance.
6. Collibra
Collibra is an enterprise data governance platform focused on policy management, stewardship, and data cataloging. In BCBS 239 programs, it is often introduced to formalize governance structures and bring visibility to data ownership and policy alignment across the organization.
How Collibra supports BCBS 239 compliance
-
Formalizes governance by defining ownership, stewardship, and policy controls for critical risk data.
-
Provides cataloging and workflow capabilities that support governance documentation during reviews.
Limitation
Collibra does not perform risk aggregation or calculation and relies on integration with other platforms for technical execution and analytics.
Collibra is often used where BCBS 239 gaps relate to formal governance structure and policy clarity, rather than traceability of data flows or evidence of transformation.
7. Oracle
Oracle provides enterprise database, data processing, and reporting infrastructure used extensively in financial services environments. Within BCBS 239 implementations, Oracle platforms often underpin the stability, performance, and control of data processing environments.
How Oracle supports BCBS 239 compliance
-
Provides stable, scalable infrastructure for processing large volumes of risk data under compressed reporting timelines.
-
Generates system logs and execution records that support evidence of operational consistency.
Limitation
Oracle does not replace data governance tooling and does not establish business ownership, stewardship, or end-to-end lineage across upstream and downstream systems.
Oracle becomes relevant in BCBS 239 discussions when questions center on processing stability, scalability, and operational reliability, not data governance or traceability.
8. Moody’s Analytics
Moody's Analytics provides risk models, analytics, and regulatory reporting solutions across credit, market, and liquidity risk. In BCBS 239 contexts, it is often used where institutions rely on standardized risk methodologies and externally supported reporting frameworks.
How Moody’s Analytics supports BCBS 239 compliance
-
Supports standardized risk models and repeatable analytical execution across portfolios and scenarios.
- Produces structured outputs aligned to regulatory reporting requirements.
Limitation
Moody’s Analytics does not provide enterprise-wide data lineage or governance across internal source systems, requiring supplementary tooling to explain data provenance.
Moody’s Analytics is most useful where BCBS 239 challenges relate to model-driven risk calculation and standardized reporting, rather than internal data control and traceability.
Taken together, these tools address different parts of the BCBS 239, but tooling alone does not explain why compliance remains such a persistent challenge.
Why BCBS 239 compliance tools are important today
Despite years of remediation, over 90% of the banks assessed by the Basel Committee were not fully compliant across all BCBS 239 principles. Each category of tool addresses a specific control expectation, from data quality to traceability.
Persistent supervisory findings and remediation pressure
Findings persist where controls are fragmented or executed inconsistently across systems and entities. When evidence relies on manual explanations, remediation efforts tend to stall. Compliance tools embed controls into daily workflows, making them repeatable and sustainable.
Increased focus on risk data accuracy and lineage
Reviews now examine how risk numbers are sourced and transformed, not just their final values. Traceability to source systems has become a baseline expectation, with system-generated lineage preferred over narrative explanations.
-
Limitations of spreadsheets and legacy risk systems
Spreadsheets and legacy platforms do not scale or reproduce results reliably under scrutiny. Manual reconciliations are difficult to defend consistently, increasing operational and compliance risk.
-
Importance of stress period and intraday risk reporting
BCBS 239 places heightened emphasis on reporting during stress and intraday cycles. Automated tools help maintain accuracy, consistency, and traceability when timelines compress and pressure increases.
These pressures make it clear that BCBS 239 compliance cannot be addressed through a single solution or control layer, and different challenges arise across the risk data lifecycle.
|
A common BCBS 239 failure pattern A common failure pattern in BCBS 239 programmes is not the absence of technology, but imbalance. Many institutions have invested heavily in specific layers, such as risk aggregation engines or regulatory reporting platforms, while governance, lineage, and ownership controls remain weak or inconsistently applied. Supervisory findings frequently arise from these mismatches. Risk numbers may calculate correctly, and reports may be delivered on time, yet institutions are unable to demonstrate where data originated, how it was transformed, or who is accountable when issues arise. In these cases, the gap is not technological capability but the lack of connected controls across the risk data lifecycle. This is why BCBS 239 compliance tools are best understood by the control outcomes they support rather than the functions they perform in isolation. |
Types of BCBS 239 Compliance Tools
BCBS 239 compliance tools are grouped by the control outcomes they support across the risk data lifecycle. Each category addresses a specific expectation, and gaps in any area can undermine overall compliance.
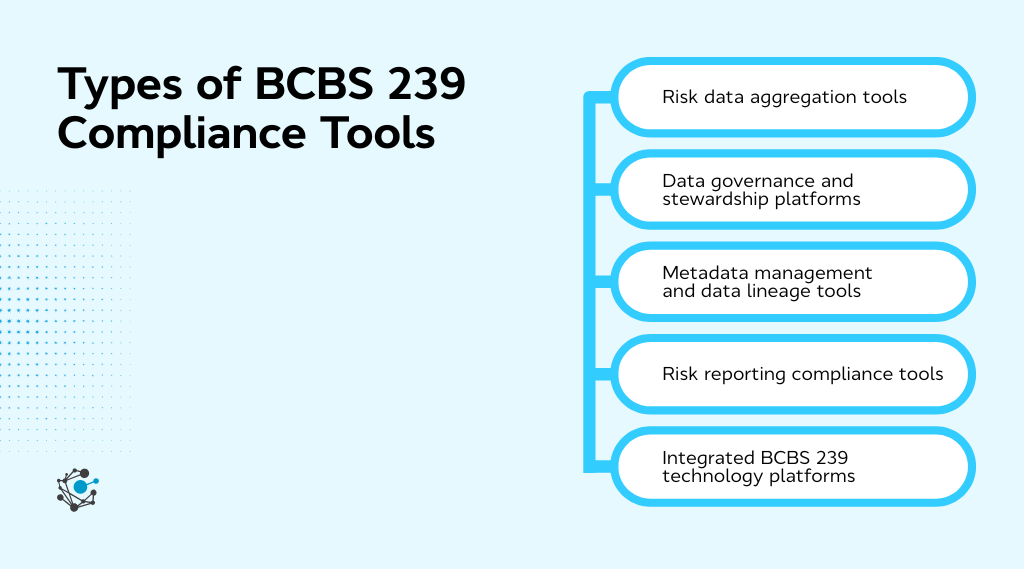
Risk data aggregation tools
Aggregate exposures and risk measures across systems and entities, supporting accurate, consistent, and repeatable aggregation, including under stress.
Data governance and stewardship platforms
Formalize ownership, accountability, and control over critical risk data used in reporting, enabling clear responsibility and escalation. Platforms such as OvalEdge can be used at this layer to connect ownership and governance to the data actually used in risk processes.
Metadata management and data lineage tools
Provide visibility into how data is defined, transformed, and moved across the environment, supporting traceability from reports back to source systems.
Risk reporting compliance tools
Support consistent and timely production of management and regulatory reports, with alignment dependent on the quality and governance of upstream data.
Integrated BCBS 239 technology platforms
Span multiple categories, but sustainable compliance still depends on clear role separation and end-to-end evidence rather than consolidation alone.
| Key takeaway: No single category provides full BCBS 239 coverage. Effective compliance requires coordinated use of these tools to produce repeatable, defensible evidence. |
What ultimately matters is whether those tools deliver the capabilities required to meet BCBS 239 expectations in practice.
Core capabilities required across the BCBS 239 risk data lifecycle
BCBS 239 compliance is not achieved by implementing isolated capabilities. Supervisory assessments focus on whether governance, aggregation, lineage, quality, and reporting controls operate together as a connected system. Strong execution in one layer does not compensate for weaknesses in others. In practice, findings often arise where capabilities exist but are fragmented, inconsistently applied, or disconnected across the risk data lifecycle.
BCBS 239 reviews, therefore, assess whether the following core capabilities operate consistently and produce repeatable, system-generated evidence.
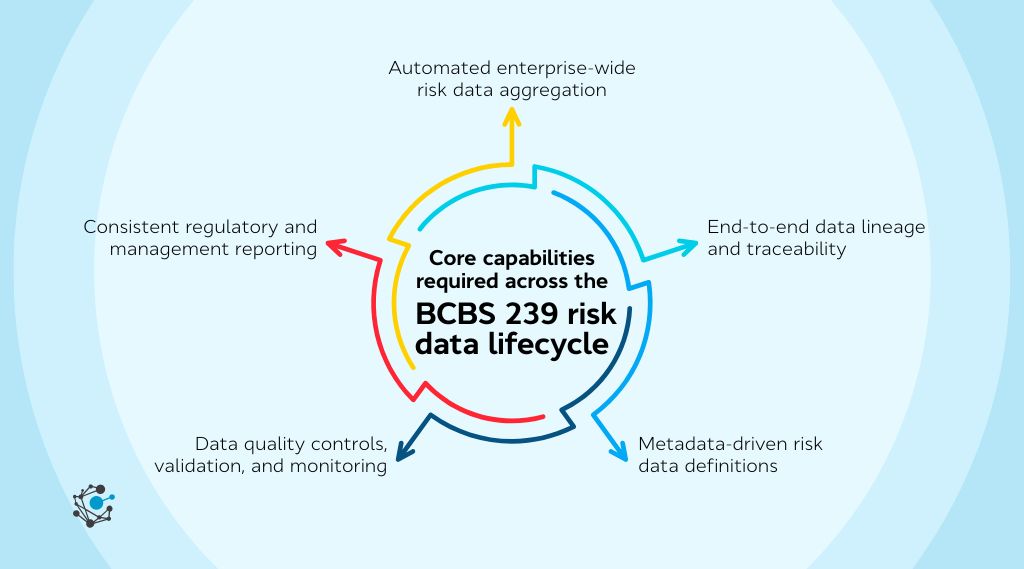
1. Automated enterprise-wide risk data aggregation
Risk data must be aggregated consistently across systems, legal entities, and risk types without manual intervention. Aggregation logic should be standardised, repeatable, and adaptable to both normal and stress conditions. Evidence is demonstrated through reproducible aggregation outputs rather than one-off reconciliations.
2. End-to-end data lineage and traceability
Reported risk numbers must be traceable back to source systems and intermediate transformations. Supervisors expect system-generated lineage that explains how data moved and changed, rather than post-hoc narratives. Gaps in upstream traceability are treated as control weaknesses even if final reports appear accurate.
|
Read More → BCBS 239 Data Lineage |
3. Metadata-driven risk data definitions
Risk metrics must be governed through centrally defined and approved metadata that is applied consistently across risk, finance, and reporting. Definitions, calculation logic, and usage context should be explicitly linked to data elements and reports. Reviews examine whether conflicting interpretations of the same metric are prevented through governed definitions rather than manual alignment.
4. Data quality controls, validation, and monitoring
Data quality checks must be defined, executed, and monitored consistently over time. Controls should operate at source and during aggregation, with issues tracked through resolution. Evidence includes rule execution results, issue histories, and demonstrable impact analysis on downstream reports.
5. Consistent regulatory and management reporting
Management and regulatory reports must be produced through controlled, repeatable workflows. Where differences exist, they must be explainable through system-based reconciliation rather than manual explanations. Consistency over time is a key indicator of control effectiveness.
Together, these capabilities define whether BCBS 239 controls function as an operating model rather than a collection of tools.
How to evaluate BCBS 239 compliance tools in practice
Evaluating BCBS 239 compliance tools requires looking beyond feature lists to how controls operate, integrate, and produce evidence. The key question is not whether a tool claims coverage of BCBS 239 principles, but whether its outputs would stand up to supervisory review without last-minute evidence reconstruction.
1. Coverage and consistency across all BCBS 239 principles
Evaluation should confirm that governance, aggregation, and reporting controls are addressed end-to-end and applied consistently across systems and entities. Tools that appear to cover multiple principles often fall short when ownership, lineage, or evidence does not extend uniformly across the risk data lifecycle. Fragmented execution is a common source of repeated findings.
2. Scalability across business lines and geographies
Controls must remain consistent as complexity increases. Tools that rely on local workarounds or manual adjustments tend to break under supervisory scrutiny. Scalable execution reduces findings related to inconsistent application across portfolios, entities, and regions.
3. Integration with risk, finance, and data platforms
Tools should integrate cleanly into the existing ecosystem rather than create parallel processes. Poor integration often forces teams into manual reconciliations when evidence is requested. Effective integration reduces operational friction and improves evidence reliability during reviews.
4. Auditability and regulatory defensibility
The most critical test is whether evidence can be produced directly from the system. Tools should generate traceable outputs that link reported numbers to source data, transformations, controls, and ownership. This is what prevents supervisory reviews from relying on explanations instead of proof.
This shift toward system-generated, review-ready outputs reflects broader expectations around data governance and regulatory defensibility. With these evaluation criteria in place, it becomes easier to assess whether BCBS 239 compliance tools will support sustainable compliance in real operating environments.
Conclusion
BCBS 239 compliance tools are essential for achieving sustainable regulatory compliance and effective risk management. Nearly a decade after BCBS 239 took effect, fewer than 10% of assessed global banks achieved full compliance across all principles. The real challenge today is not understanding the principles but making them work consistently in day-to-day operations.
BCBS 239 has effectively become an operating model rather than a one-time project. Reviews now look for proof that risk data can be aggregated, traced, validated, and reproduced on demand, including during stress. Diagrams and policy documents still matter, but they carry far less weight than evidence generated directly from systems.
If you are stepping back to assess whether your BCBS 239 controls would stand up to review today, it is often useful to look first at traceability, ownership, and evidence gaps. This is where OvalEdge is frequently evaluated to strengthen governance and lineage capabilities and reduce reliance on manual explanations.
Note: All quantitative BCBS 239 statistics cited in this article are sourced from Basel Committee on Banking Supervision progress assessments.
FAQs
1. Which banks are required to comply with BCBS 239?
BCBS 239 primarily applies to global and domestic systemically important banks, but many regulators expect similar standards from other large and complex financial institutions.
2. Can a single tool ensure full BCBS 239 compliance?
No single tool can address all BCBS 239 requirements. Most banks use a combination of risk aggregation, data governance, metadata, lineage, and reporting tools to achieve sustainable compliance.
3. How do regulators assess BCBS 239 compliance?
Regulators assess compliance through supervisory reviews, stress testing exercises, data quality evaluations, and the bank’s ability to provide clear lineage and evidence supporting risk reports.
4. Is BCBS 239 compliance a one-time implementation?
BCBS 239 compliance is an ongoing operational capability. Banks are expected to continuously maintain, monitor, and improve their risk data aggregation and reporting processes.
5. How long does it take to achieve BCBS 239 compliance?
Timelines vary based on data complexity and existing infrastructure, but most banks treat BCBS 239 as a multi-year program. Initial compliance may take 12–24 months, while sustainable, regulator-ready compliance requires ongoing investment and refinement.
Deep-dive whitepapers on modern data governance and agentic analytics

OvalEdge Recognized as a Leader in Data Governance Solutions
.png?width=1081&height=173&name=Forrester%201%20(1).png)
“Reference customers have repeatedly mentioned the great customer service they receive along with the support for their custom requirements, facilitating time to value. OvalEdge fits well with organizations prioritizing business user empowerment within their data governance strategy.”
.png?width=1081&height=241&name=KC%20-%20Logo%201%20(1).png)
“Reference customers have repeatedly mentioned the great customer service they receive along with the support for their custom requirements, facilitating time to value. OvalEdge fits well with organizations prioritizing business user empowerment within their data governance strategy.”
Gartner, Magic Quadrant for Data and Analytics Governance Platforms, January 2025
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
GARTNER and MAGIC QUADRANT are registered trademarks of Gartner, Inc. and/or its affiliates in the U.S. and internationally and are used herein with permission. All rights reserved.