Table of Contents
Data Discovery Techniques for Enterprise Teams: Methods, Tools, and Best Practices
Modern data environments evolve faster than manual controls can keep up. This blog explains how advanced data discovery techniques move beyond periodic scans to continuous, governance-aligned automation. It covers metadata ingestion, profiling, AI-driven classification, lineage mapping, predictive discovery, and maturity metrics that define scalable programs. You will learn how enterprise platforms operationalize discovery through unified metadata architecture and workflow-driven governance. The result is a measurable, defensible, automation-first discovery strategy built for AI-scale complexity.
A governance team recently completed what they believed was a comprehensive data inventory. Weeks later, a new SaaS integration introduced additional customer attributes into a warehouse table, and those fields quietly flowed into dashboards used across the business.
Nothing malicious happened. The environment simply evolved faster than the controls. This is a common pattern. Enterprise data now spans cloud platforms, SaaS applications, and on-prem systems, changing daily through new pipelines and integrations.
In its 2024 report “Charting a Path to the Data- and AI-Driven Enterprise of 2030,” McKinsey highlights that organizations scaling AI successfully rely heavily on automation to manage complexity and reduce manual intervention.
That same principle applies to discovery. Modern data discovery techniques must operate continuously, not periodically. In this guide, we break down how advanced, governance-aligned techniques are operationalized at scale.
What are data discovery techniques?
Data discovery techniques are the technical mechanisms that make discovery work inside modern data ecosystems. They are the engines that identify assets, profile content, classify sensitivity, and keep everything current as data changes.
This is different from the data discovery process, which is the sequence of steps your organization follows. It is also different from data discovery methods, which are categories of approaches. Techniques are what you operationalize in tools and pipelines so discovery can run continuously, at scale, without depending on heroics.
Because these techniques run continuously across systems, they become foundational components of enterprise data architecture. They integrate with data catalogs, governance platforms, security controls, and data pipelines to ensure sensitive assets are consistently identified, classified, and governed across hybrid and multi-cloud environments.
Core data discovery techniques used in modern enterprises
Modern enterprises no longer rely on a single scan or catalog update to understand their data landscape. Instead, they operationalize multiple, complementary data discovery techniques that work together to create continuous visibility, contextual intelligence, and governance alignment.
The techniques below form the technical backbone of scalable discovery in complex, distributed environments.
Metadata ingestion and structural mapping
Most enterprise data discovery techniques begin with metadata. It is fast to collect, low risk compared to full data scans, and highly scalable across distributed systems.
Modern connectors extract:
-
Schemas from databases and data warehouses
-
API-level metadata from SaaS platforms
-
Object and file structures from storage systems and catalogs
The real value emerges when this metadata is normalized into a consistent model. Once standardized, teams can search, govern, and analyze data assets across environments without being constrained by system-specific formats.
In practice, this enables true system-wide visibility. Governance leaders can quickly answer critical operational questions:
-
Which systems store customer identifiers
-
Which datasets are actively used or dormant
-
Where redundant or shadow copies exist
This foundation is also reflected in how the market evaluates modern catalog platforms.
|
Example: According to Forrester’s Data Governance Market Trends 2024 report, effective data governance requires centralized oversight and the elimination of silos, both of which depend on consistent and well-managed metadata. |
Data profiling and quality assessment
Once you know what data exists, the next step is understanding what is inside it and whether it can be trusted. Data profiling evaluates key quality dimensions such as completeness, uniqueness, consistency, and timeliness.
Modern profiling techniques automatically:
-
Measure null values and missing records
-
Detect duplicate entries and unstable keys
-
Identify out-of-range or structurally inconsistent values
-
Highlight unexpected distribution shifts
This is where data discovery moves from inventory to intelligence. Profiling transforms a list of datasets into actionable insight by revealing reliability risks before they affect reporting or analytics.
In practice, profiling signals are often straightforward but highly impactful. An “email” field that suddenly becomes 40 percent null after a pipeline update, or a primary key that loses uniqueness due to transformation changes, can compromise dashboards, machine learning models, and compliance reporting.
By continuously monitoring these indicators, organizations strengthen trust in their data and prioritize remediation where it matters most.
Automated sensitive data detection
Automated sensitive data detection is where discovery directly impacts risk management. Modern engines scan structured and unstructured data to identify regulated attributes at scale.
These systems combine:
-
Pattern-based detection for common identifiers
-
Contextual analysis to reduce misclassification
-
Named entity recognition for unstructured content
-
Confidence scoring to validate results
Scalability depends on evidence capture. Instead of simply labeling a field as sensitive, the system records why it was classified and how confident the model is. This reduces false positives, limits alert fatigue, and makes classifications defensible.
By linking detection outputs to governance and compliance controls, organizations move from passive scanning to actionable risk oversight.
Context-aware classification using metadata and lineage
Detection alone is not enough. Enterprise-ready classification requires context, including business meaning, ownership, usage patterns, and downstream impact. Metadata and lineage transform raw detection signals into governance-aware decisions.
Context-aware classification incorporates:
-
Business glossary definitions and domain ownership
-
System purpose and data usage patterns
-
Table naming conventions and structural signals
-
Upstream sources and downstream dependencies from lineage
For example, two columns may both match an email pattern. One may be a hashed internal routing identifier, while the other contains actual customer emails used for communication. Context determines how each is classified, what controls apply, and how retention is enforced.
AI increasingly supports this layer by combining pattern detection with metadata and lineage insights.
|
Do you know: According to McKinsey’s 2024 insights on the future of data and AI-driven enterprises, generative AI and automation are beginning to take over tasks such as data classification and are expected to expand into more sophisticated capabilities, including aspects of lineage production over time. |
Lineage mapping for relationship visibility
Lineage is the technique that makes discovery explainable. It helps you trace upstream sources, understand transformation logic, and identify downstream dependencies.
|
For governance leaders, lineage is often the difference between “we think we know” and “we can prove it.” |
Operationally, lineage mapping improves impact analysis. When a sensitive field is introduced or reclassified, you can see where it flows, which reports use it, and where controls must be updated. That is how discovery becomes continuous and actionable rather than purely informational.
Automation techniques for continuous discovery
Discovery cannot remain static in environments where data structures, integrations, and usage patterns change daily. To operate at enterprise scale, data discovery techniques must move from scheduled scans to event-driven, intelligent automation that adapts to change in real time.
Automation transforms discovery from a periodic activity into a continuous governance capability, reducing blind spots, accelerating response times, and ensuring that risk visibility keeps pace with business growth.
Continuous schema monitoring
Schema drift is a common reason discovery breaks at scale. Columns are added, renamed, or repurposed, and new tables or SaaS fields appear without notice.
Continuous schema monitoring:
-
Detects structural changes automatically
-
Triggers reclassification where needed
-
Flags high-risk updates for steward review
Treat schema change as a governance event, not just an engineering update. Automated workflows should capture what changed, what classifications are impacted, and which downstream assets are affected.
Anomaly detection in data behavior
Discovery is not only about what data is. It is also about how data behaves. Behavioral anomaly detection watches signals like unusual access patterns, sudden spikes in extraction volume, or unexpected distribution shifts that indicate a pipeline issue, misuse, or policy drift.
This is where discovery starts to overlap with observability and security, and that is a good thing. When governance and security teams share the same discovery layer, risk triage becomes faster and less political.
Predictive discovery using machine learning
Predictive discovery is the next layer: using machine learning to anticipate where risk and quality problems will emerge. The practical use cases are more grounded than they sound:
-
Forecasting quality degradation based on past incidents and pipeline changes
-
Predicting where sensitive attributes are likely to appear based on source systems and transformation patterns
-
Prioritizing rescans by risk, usage, and exposure rather than on a calendar
According to BCG’s 2024 insights on modern data management, AI can significantly reduce the manual burden of governance and data management when it is thoughtfully embedded into operational workflows.
This is one of the most useful places to apply it, because it reduces wasted scanning and focuses attention where the enterprise actually has exposure.
Governance-driven discovery techniques
Discovery only becomes strategic when it is directly connected to governance controls. At scale, data discovery techniques must not only detect and classify data, but also trigger policies, enforce accountability, and create defensible records.
Policy-linked classification and control mapping
This is where discovery shifts from labeling data to enforcing controls. Classification tags should activate governance actions, not just sit in a catalog. A policy-linked approach connects sensitivity levels to access rules, retention policies, and masking requirements.
In mature environments, a high-sensitivity tag can automatically require approvals for data sharing, enforce restricted access by default, and initiate retention or deletion workflows. Governance becomes operational when classification decisions directly drive control enforcement.
Human-in-the-loop validation
Automation alone cannot guarantee accuracy. Human-in-the-loop validation ensures that discovery results are reviewed, corrected, and improved over time. Low-confidence classifications are routed to stewards, and their decisions are captured as structured feedback.
This approach balances efficiency with accountability. It builds trust in automated systems while continuously refining detection and classification logic based on real-world oversight.
Audit-ready documentation and traceability
Audit readiness must be embedded into the discovery process. Every classification decision, change, and approval should be logged with timestamps and accountable owners.
Traceability ensures organizations can explain what data exists, how it is classified, what controls apply, and how decisions were made. This turns discovery into defensible evidence rather than a static inventory.
Maturity progression in data discovery techniques
Data discovery does not evolve all at once. It progresses through clear stages, moving from manual documentation to intelligent, risk-based automation.
Understanding this maturity curve helps governance leaders assess where they stand today and what capabilities must be strengthened to scale responsibly.
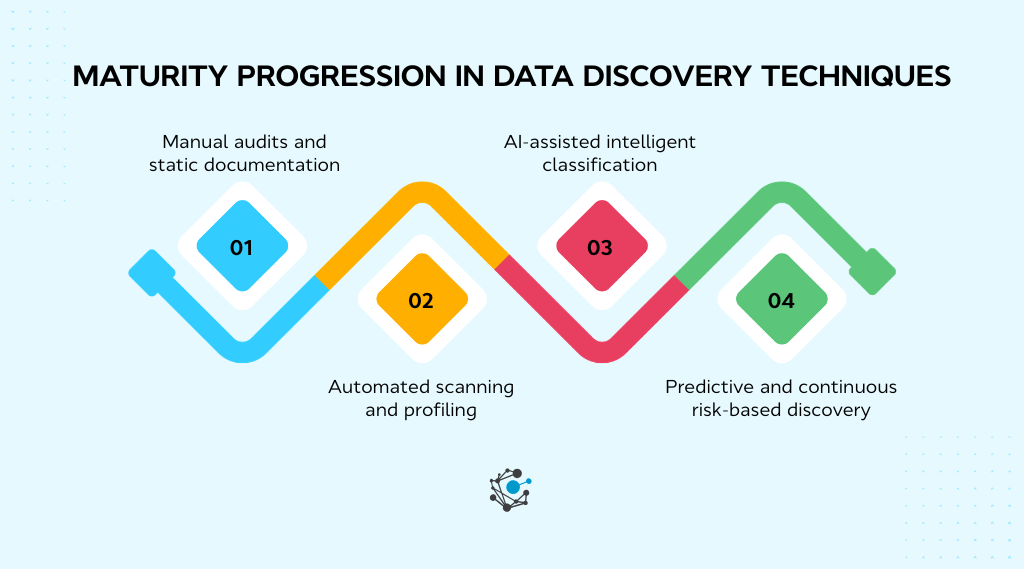
Stage 1: Manual audits and static documentation
This stage is spreadsheet-heavy and interview-driven. It can work for a small environment, but it collapses when data grows and changes daily.
Stage 2: Automated scanning and profiling
Here, you get connectors, scheduled scans, and profiling. You move from manual inventory to automated visibility. The common gap is that outputs still sit in dashboards rather than driving controls.
|
Strengthening Discovery with Lineage OvalEdge’s Data Lineage: Benefits and Techniques whitepaper offers deep insights into harnessing lineage for scalable impact analysis. |
Stage 3: AI-assisted intelligent classification
Now classification incorporates context, lineage, and feedback loops. AI reduces false positives and prioritizes what needs attention. McKinsey’s broader direction of automation taking over classification tasks aligns with why this stage is becoming normal in large enterprises.
Stage 4: Predictive and continuous risk-based discovery
This stage is continuous, event-driven, and risk-based. You scan and reclassify based on change signals, usage, exposure, and predicted risk. Governance becomes a living system, not a periodic program.
How enterprise platforms operationalize advanced discovery techniques
Advanced data discovery techniques only deliver value when they are embedded into a scalable platform architecture. Enterprise environments require more than scanning. They require unified metadata, embedded intelligence, and workflow-driven governance.
What distinguishes governance-native platforms like OvalEdge is that discovery outputs immediately activate governance workflows. Classification results trigger stewardship assignments, lineage-based impact analysis, and policy enforcement automatically.
This ensures discovery becomes an operational control layer rather than a passive metadata collection process.
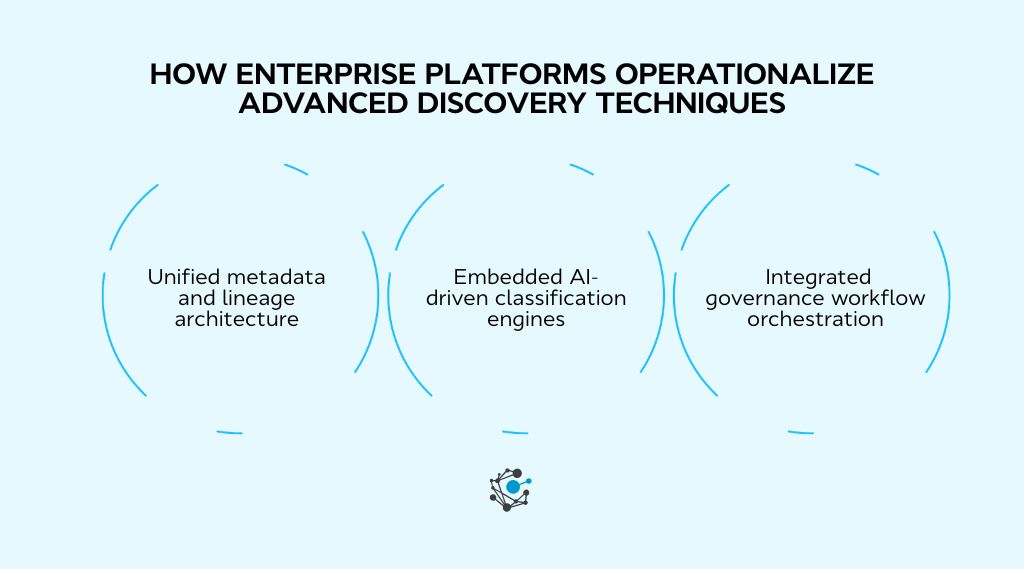
Unified metadata and lineage architecture
Enterprise discovery begins with consolidation and normalization. OvalEdge centralizes technical, operational, and business metadata across the data ecosystem.
Centralized ingestion
OvalEdge connects to databases, warehouses, lakes, ETL tools, and BI platforms to extract:
-
Schemas, tables, and columns
-
Data relationships and dependencies
-
Usage and ownership metadata
By normalizing this information into a single metadata repository, organizations gain system-wide visibility instead of fragmented discovery results.
Real-time metadata synchronization
To manage schema drift and rapid changes:
-
New tables and columns are captured quickly
-
Schema alterations trigger metadata refresh
-
Discovery coverage remains current
This reduces the gap between data creation and governance awareness.
Cross-system visibility through lineage
OvalEdge’s end-to-end lineage connects:
-
Upstream data sources
-
Transformation logic
-
Downstream reports and dashboards
This context strengthens classification decisions and improves risk impact analysis. When sensitive data is detected, teams can immediately see where it flows and who consumes it.
|
Related reading: Enterprise Metadata Management Strategy explains why metadata architecture is the backbone of scalable governance and automated discovery |
Embedded AI-driven classification engines
Automation at scale requires more than pattern matching. OvalEdge integrates AI-assisted discovery with contextual intelligence.
Continuous scanning
OvalEdge supports automated sensitive data discovery across structured and semi-structured sources:
-
Pattern-based detection for regulated identifiers
-
Scheduled or continuous scanning
-
Configurable discovery rules
This enables broad discovery coverage without manual audits.
Context-aware tagging
Detection results are enhanced using:
-
Business glossary alignment
-
Domain ownership mapping
This layered approach reduces false positives and increases classification accuracy compared to standalone detection engines.
Human-in-the-loop validation
OvalEdge balances automation with accountability:
-
Low-confidence classifications are routed to stewards
-
Overrides are logged with justification
-
Classification decisions improve over time
This creates a defensible and auditable discovery process.
Integrated governance workflow orchestration
Operational discovery must connect directly to governance controls. OvalEdge integrates classification results with enforcement workflows.
Policy enforcement and control mapping
Discovery outputs can be aligned with:
-
Data sensitivity levels
-
Access review processes
-
Masking and retention policies
This ensures classified data is not just labeled but governed.
Stewardship workflows
OvalEdge supports structured governance workflows:
-
Task assignments to data owners
-
SLA-based reviews
-
Exception tracking and audit logs
This formalizes accountability across domains.
|
Strategic Insight: Governance-led platforms such as OvalEdge emphasize unified metadata ingestion and lineage visibility as core capabilities, positioning centralized transparency as foundational to enterprise governance. |
Cross-team visibility
OvalEdge provides a shared metadata layer where:
-
Security teams monitor sensitive data exposure
-
Data architects analyze lineage impact
-
Compliance teams generate audit-ready reports
Discovery insights become accessible enterprise-wide, not isolated within governance functions.
When Enterprises Must Adopt Advanced Discovery Techniques
Organizations typically adopt advanced discovery techniques when manual inventories and periodic scans no longer scale with data growth.
Common triggers include:
-
Regulatory compliance requirements such as GDPR, HIPAA, or financial reporting obligations
-
Cloud migrations introducing new data pipelines, warehouses, and storage environments
-
AI and analytics initiatives requiring trusted, classified datasets
-
Rapid SaaS adoption is creating fragmented data ownership and shadow data
-
Governance programs demanding continuous classification and lineage visibility
At this stage, discovery techniques must operate continuously rather than periodically. They must integrate directly with governance workflows, security controls, and metadata systems to ensure that new data assets are identified, classified, and governed as soon as they appear.
Key metrics to evaluate discovery technique maturity
Advanced data discovery techniques should be measured like operational systems, not feature checklists.
The following metrics help governance leaders and data architects evaluate whether their discovery process is scalable, accurate, and aligned with enterprise risk management.
-
Discovery Coverage Percentage: Measures the proportion of data assets actively scanned and monitored across systems. High maturity means broad coverage across structured, semi-structured, cloud, SaaS, and on-prem environments.
-
Classification Accuracy Rate: Indicates how often automated classifications match validated ground truth. Mature programs continuously refine models and rules to improve precision across data categories.
-
False Positive and False Negative Ratios: Tracks detection quality by separating overclassification from missed sensitive data. Advanced teams monitor both to balance operational efficiency with compliance risk reduction.
-
Time-to-Detection for Sensitive Data: Measures how quickly newly created or ingested sensitive data is identified and classified. Shorter detection windows reduce governance gaps and exposure risk.
-
Reclassification Latency: Evaluates how fast classifications update after schema changes or lineage shifts. Low latency reflects a continuous discovery architecture rather than periodic audits.
-
Audit Readiness Score: A composite metric combining ownership assignment, policy mapping, lineage completeness, and decision logging. High scores indicate defensible, compliance-ready discovery programs.
These metrics transform data discovery from a static cataloging activity into a measurable, continuously improving governance capability.
Conclusion
As regulatory pressure increases, cloud ecosystems expand, SaaS adoption accelerates, and AI initiatives demand trusted data, manual discovery models stop scaling. Enterprises must shift from periodic scanning to continuous, governance-driven discovery techniques that evolve with their architecture.
Advanced discovery is no longer about cataloging assets. It is about integrating metadata, profiling, lineage, and AI-assisted classification directly into policy enforcement, access controls, and audit workflows.
OvalEdge operationalizes this model by unifying metadata ingestion, lineage visibility, intelligent classification, and governance orchestration within a centralized platform. Discovery results immediately activate stewardship, policy mapping, and compliance controls.
By embedding continuous, risk-aware discovery into enterprise architecture, organizations reduce blind spots, strengthen audit readiness, and scale data innovation without sacrificing control.
Book a demo with OvalEdge to see how a governance-native platform can operationalize advanced data discovery and transform visibility into enforceable, scalable control.
FAQs
1. How accurate are AI-driven classification techniques?
Accuracy depends on signal diversity and feedback loops. Techniques that combine content pattern detection, metadata context, and lineage relationships typically outperform single-layer approaches. Mature programs validate samples regularly and refine rules based on steward decisions to continuously improve precision.
2. What reduces false positives in automated discovery?
False positives decrease when detection is context-aware. Combining pattern matching with glossary alignment, domain ownership mapping, and lineage insights improves confidence scoring. Ongoing steward validation and rule tuning are essential to prevent alert fatigue while maintaining coverage.
3. Can predictive discovery prevent compliance violations?
Predictive discovery can reduce exposure windows when integrated with enforcement workflows. If risk signals trigger early access restrictions, masking, or review workflows, organizations can mitigate issues before sensitive data spreads downstream.
4. How does lineage improve classification accuracy?
Lineage adds business and technical context. If a downstream column is derived from a confirmed sensitive source, classification confidence increases. Lineage also enables impact-aware tagging by showing where sensitive data flows and who consumes it.
5. What metrics indicate mature discovery programs?
Mature programs demonstrate high discovery coverage, strong classification accuracy, low false negative ratios, short time-to-detection, low reclassification latency, and strong audit readiness scores. Improvement trends over time matter more than static numbers.
6. How often should continuous discovery scans run?
The frequency should match the pace of change in your environment. High-velocity systems benefit from event-driven or near real-time scanning. More stable environments can use scheduled scans, but intervals should be short enough to minimize governance gaps.
Deep-dive whitepapers on modern data governance and agentic analytics

OvalEdge Recognized as a Leader in Data Governance Solutions
.png?width=1081&height=173&name=Forrester%201%20(1).png)
“Reference customers have repeatedly mentioned the great customer service they receive along with the support for their custom requirements, facilitating time to value. OvalEdge fits well with organizations prioritizing business user empowerment within their data governance strategy.”
.png?width=1081&height=241&name=KC%20-%20Logo%201%20(1).png)
“Reference customers have repeatedly mentioned the great customer service they receive along with the support for their custom requirements, facilitating time to value. OvalEdge fits well with organizations prioritizing business user empowerment within their data governance strategy.”
Gartner, Magic Quadrant for Data and Analytics Governance Platforms, January 2025
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
GARTNER and MAGIC QUADRANT are registered trademarks of Gartner, Inc. and/or its affiliates in the U.S. and internationally and are used herein with permission. All rights reserved.